In Hacking the main focus is over gathering the information about victim or victim's machine. Which will help to find out which type of exploit will works according to the given circumstances. Gathering the network and host information means to find out by which network, the which victim's machine is connected and communicating over the network. Moreover, scanning is also performed for gathering information about open and closed ports. After that they'll able to find the vulnerabilities in the target system and try to get access to the system.
Types Of Scan
As a CEH you should know the scan types and uses:SYN
SYN scan doesn't complete the TCP three way handshake that is why it is known as a half-open scan. An attacker send a SYN packet to the victim machine if SYN/ACK packet is received back to attacker, then it clarify that the port is listening due to the acknowledgment by the victim that it has completed the connection. While if the attacker is received the RST/ACK packet then it assumed that the port is closed or open.XMAS
XMAS scan works only on target system that has the RFC 793 development of TCP/IP and it doesn't works against any version of windows.XMAS scan send a packet with by setting up the FIN, URG and PSH flags of the TCP header. The function of this scan is if the port is active there will be no response but if the port is closed the target responds with a RST/ACK packet.
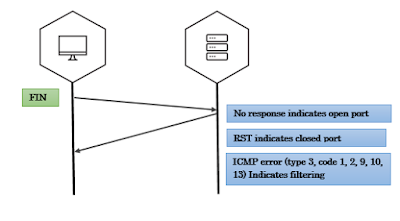
FIN
A FIN scan send a packet by setting up only the FIN flag of the TCP. This scan is similar to XMAS scan. FIN scan receives no response if the port is active while if the port is closed it receives the RST/ACK packet.NULL
NULL scan is also similar to the XMAS scan. But the only difference is that it sends a packet without setting up the any flag of TCP header. NULL scan receives no response if the port is open but if the port is closed it receives the RST/ACK packet.IDLE
It is just like spoofing an IP address by sending a SYN packet to the victim's machine to find out which services are available over the system. This scan is completed with the help of another system called as "Zombie" (that is not receiving or transmitting any information).Related word
- Hacker Tools For Ios
- Hack Website Online Tool
- Hacking Tools Free Download
- Hacking Tools Github
- Kik Hack Tools
- Hack Tools 2019
- Pentest Tools Windows
- New Hacker Tools
- Hacker Tools Apk Download
- Github Hacking Tools
- Free Pentest Tools For Windows
- Best Pentesting Tools 2018
- Hack Tools
- Pentest Tools Download
- Hacking Tools Windows
- Tools Used For Hacking
- Hacker Tools For Ios
- Hack Tools For Pc
- Hacking Tools Download
- Pentest Tools Linux
- Hack Website Online Tool
- Nsa Hack Tools
- Hack Tools For Mac
- Hacker Tools
- Pentest Tools Framework
- Pentest Tools Download
- Pentest Automation Tools
- Hacker Search Tools
- Hacker Hardware Tools
- Hack Tool Apk
- Hack Tool Apk No Root
- Hack Tools 2019
- Hack Tools Online
- Hacker Tools Online
- Hacker Tools Apk
- Pentest Reporting Tools
- Pentest Recon Tools
- Physical Pentest Tools
- Pentest Tools Bluekeep
- Hacks And Tools
- Hackers Toolbox
- Pentest Tools For Mac
- Hak5 Tools
- Hacker Tools Online
- Pentest Tools Online
- Hack Apps
- Wifi Hacker Tools For Windows
- Hacking Tools 2020
- Hacker Search Tools
- Hacking Tools
- Pentest Tools Free
- Hacking Tools For Mac
- Hacking Tools For Pc
- Hack Tools 2019
- Hacking Tools For Games
- Hack App
- Beginner Hacker Tools
- Pentest Tools Android
- New Hack Tools
- Hacking Tools For Pc
- Pentest Tools Android
- Hack Tools
- Hack Tools For Games
- Pentest Tools Kali Linux
- Hacking Tools Name
- Free Pentest Tools For Windows
- Ethical Hacker Tools
- Hacking Tools Online
- Hacker Tools Mac
- Hacking Tools For Windows Free Download
- Hacking Tools For Beginners
- Hacker Tools Apk
- Hacking Tools For Windows
- Pentest Tools List
- Hack Rom Tools
- Pentest Tools Port Scanner
- Pentest Automation Tools
- Android Hack Tools Github
- Nsa Hack Tools Download
- Hacking Tools 2020
- Pentest Tools Subdomain
- Hacker Tools 2019
- Nsa Hacker Tools





No comments:
Post a Comment